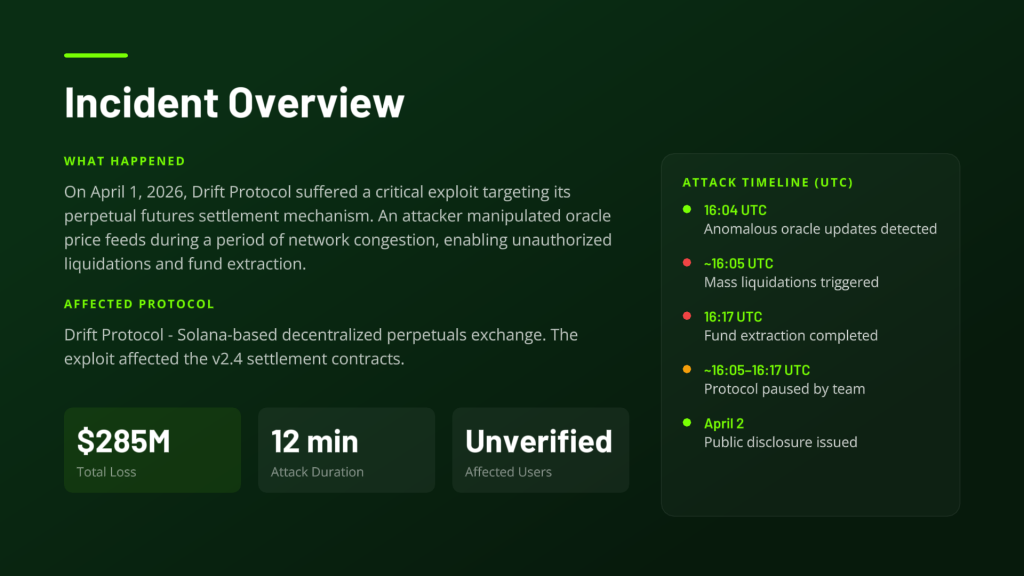
On April 1, 2026, attackers drained approximately $285 million in user assets from Drift Protocol, the largest decentralized perpetual futures exchange on Solana in roughly 12 minutes. According to DefiLlama, Drift’s total value locked collapsed from approximately $550 million to under $250 million following the attack, making it the largest DeFi hack of 2026 to date and the second-largest security incident in the Solana ecosystem after the $326 million Wormhole bridge exploit in 2022.
Drift confirmed that “a malicious actor gained unauthorized access to Drift Protocol through a novel attack involving durable nonces, resulting in a rapid takeover of Drift’s Security Council administrative powers.” The attack did not exploit any smart contract code. Trail of Bits audited Drift in 2022, and ClawSecure audited it in February 2026. Neither review identified the governance weaknesses that made the attack possible.
The Six-Month Operation
The on-chain execution on April 1 was the final step of a much longer campaign. Starting in or about fall 2025, individuals posing as a quantitative trading company approached Drift contributors at a major cryptocurrency conference under the pretext of integrating the protocol.
What followed was textbook onboarding: the group was technical, they knew the protocol, and a Telegram group was set up immediately. From there, they spent months in substantive conversations about trading strategies and vault integrations. They met Drift contributors in person at multiple conferences across multiple countries. By December 2025, they had onboarded an Ecosystem Vault, deposited over $1 million of their own capital, and held multiple working sessions with the team.
By the time April came, the relationship was nearly six months old. This was not a phishing email, these were people contributors had met repeatedly, face to face, in multiple countries.
How Devices Were Compromised
Drift’s April 5 update identified multiple potential intrusion vectors.
One contributor may have been compromised after cloning a code repository shared by the group as part of efforts to deploy a frontend for their vault. The repository-based intrusion is assessed to have involved a malicious VSCode project that weaponizes the “tasks.json” file to automatically trigger execution of malicious code upon opening the project in the IDE, using the “runOn: folderOpen” option. This technique had been adopted by North Korean threat actors associated with the Contagious Interview campaign since December 2025, prompting Microsoft to introduce new security controls in VSCode versions 1.109 and 1.110.
A second contributor was persuaded to download a wallet product via Apple’s TestFlight to beta test the app. In both cases, the malware appeared to operate silently. Right as the exploit executed on April 1, the group’s Telegram chats went dark and their malicious software was scrubbed from affected devices. Mandiant is conducting full forensic analysis.
The On-Chain Execution
On-chain staging began on March 11, nearly three weeks before April 1, with a withdrawal of 10 ETH from Tornado Cash. These funds began moving hours later at approximately 12:00 AM GMT on March 12 around 09:00 Pyongyang time and shortly after funded the deployment of CarbonVote (CVT), the token used to manipulate Drift’s oracle.

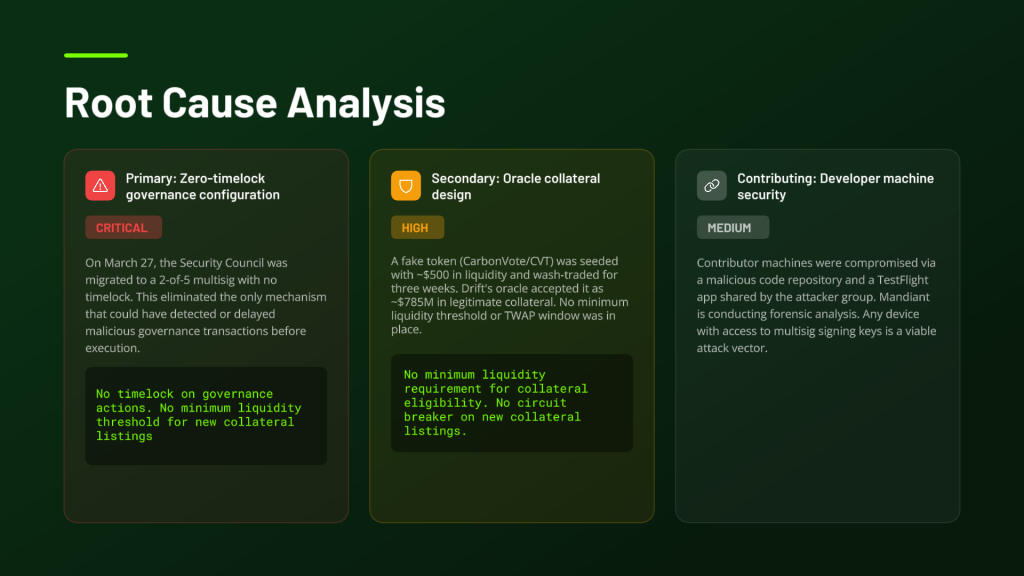
The attacker manufactured an entirely fictitious asset with a few thousand dollars in seeded liquidity and wash trading, and Drift’s oracles treated it as legitimate collateral worth hundreds of millions of dollars. The oracle lacked minimum liquidity requirements or circuit breakers that could have flagged the new collateral listing.
With machine access obtained and signing keys reachable, the attackers obtained the two multisig approvals needed to enable the durable nonce attack. Those pre-signed transactions sat dormant for more than a week before being executed on April 1, draining funds from the protocol’s vaults in under a minute.
A critical enabling factor was a governance change four days before the attack. The attack leveraged both a multisig migration changed to 2/5 without a timelock weeks earlier and untested protocol updates. Removing the timelock eliminated the one mechanism that could have given Drift’s team or the wider community a window to detect and intervene.
Fund Movement
TRM Labs noted the post-hack laundering exceeded the pace of the Bybit exploit in 2025 in both speed and transaction size. The stolen assets were swapped to USDC via Jupiter, bridged to Ethereum through Circle’s CCTP, and converted to approximately 129,000 ETH across four wallets.
Circle’s CCTP processed a large volume of stolen USDC over several hours during US business hours without a freeze being triggered. It should be noted that freezing stolen funds requires legal authority and coordination with law enforcement; this is a different process than the court-ordered freezes Circle has executed in other cases, and the comparison requires that context to be made fairly.
Attribution
Drift attributed the attack with medium confidence to UNC4736, also tracked as AppleJeus, Citrine Sleet, Golden Chollima, and Gleaming Pisces, a North Korean state-affiliated group with a history of targeting the cryptocurrency sector since at least 2018. The group is best known for the X_TRADER/3CX supply chain breach in 2023 and the $53 million hack of Radiant Capital in October 2024.
The basis for the attribution is both on-chain, fund flows used to stage and test the operation trace back to the Radiant attackers and operational, as personas deployed across the campaign have identifiable overlaps with known DPRK-linked activity.
One important nuance: the individuals who appeared in person at conferences were not North Korean nationals. State actors operating at this level are known to deploy third-party intermediaries with fully constructed identities, employment histories, and professional networks built to withstand due diligence. Mandiant has not formally attributed the exploit yet, as device forensics are still underway.
Elliptic noted that if confirmed, this would represent the eighteenth DPRK-linked crypto incident of 2026, with more than $300 million stolen to date. DPRK-linked actors are believed to have stolen over $6.5 billion in cryptoassets in recent years, with the US government linking this activity to the funding of weapons programs.
What Failed and Why
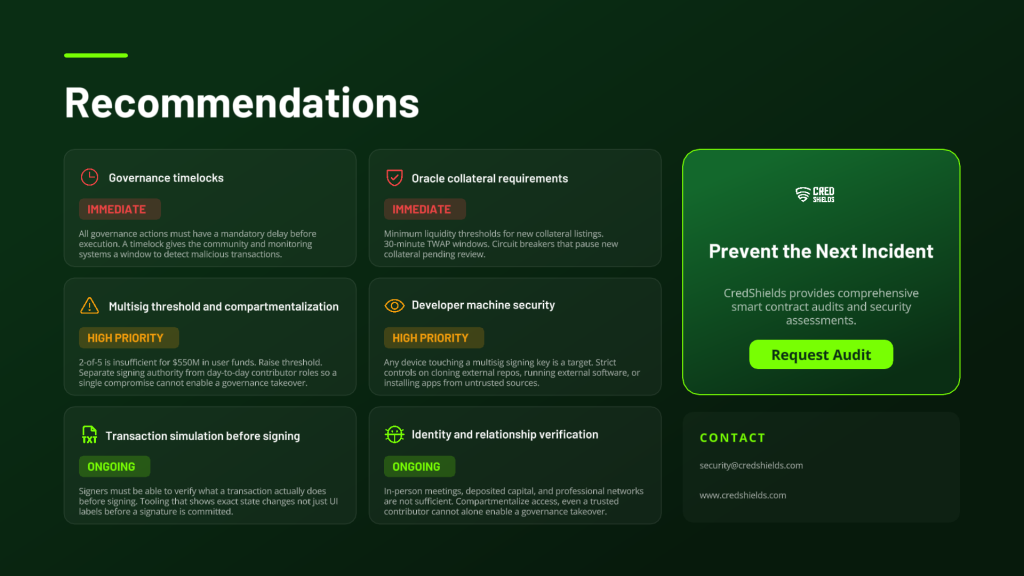
Oracle design. A $500 liquidity pool with three weeks of wash-traded price history was accepted as collateral for hundreds of millions in protocol assets. Minimum liquidity thresholds, longer TWAP windows, and circuit breakers on new collateral listings are all known fixes that were not in place.
Governance configuration. A 2/5 multisig threshold is widely considered insufficient for a protocol holding this level of user assets. More critically, the removal of the timelock on governance actions in late March eliminated any detection window between a malicious transaction being submitted and it executing. This change was made without a public governance vote.
Developer machine security. The Drift team’s use of isolated devices for communications may have prevented greater losses; had malicious files been opened on core servers, the full extent of the protocol’s assets might have been stolen. However, the attack demonstrated that any device with access to multisig signing keys is a viable attack target, and that standard antivirus tooling may not detect purpose-built, freshly compiled malware.
Identity verification. The attackers defeated every reasonable due-diligence check available to a DeFi protocol team: in-person meetings, deposited capital, professional credentials, and months of substantive technical engagement. The industry does not currently have strong answers for this threat model. Compartmentalization of access so that no single compromise can enable a governance takeover is the structural response available now.

What Remains Uncertain
Several things are still unresolved as of publication. Mandiant’s full forensic analysis is ongoing and has not formally attributed the attack. The exact moment of key compromise is unknown. It is unclear how many devices were affected beyond the two identified vectors. Fund recovery prospects are uncertain, though Drift sent on-chain messages to wallets holding the stolen ETH requesting dialogue. Whether the March 27 timelock removal was itself part of the attack chain or an independent governance decision that happened to be exploited has not been confirmed.
Broader Context
This attack fits a clear pattern. North Korean crypto operations have used social engineering as the main catalyst for many of their intrusions. This includes the recent supply chain compromise of the npm package Axios, as well as ongoing campaigns like Contagious Interview and IT worker fraud.
The progression across recent major hacks is worth stating plainly: Radiant Capital in 2024 involved device compromise through document-based malware. Bybit in early 2025 involved UI poisoning of a multisig interface. Drift in April 2026 involved a six-month in-person intelligence operation culminating in developer machine compromise and durable nonce governance takeover. Each attack was more operationally sophisticated than the last, and each exploited the gap between what protocols audit and how they actually operate day to day.
Smart contract code at major DeFi protocols is meaningfully more secure than it was five years ago. The attack surface has moved up the stack to governance, to signers, and now to the people building the protocols themselves.
Sources: Drift Protocol official incident disclosures (April 1 and April 5, 2026); TRM Labs; Elliptic; The Hacker News; CoinDesk; Bloomberg; Fortune; Mandiant attribution background via multiple outlets. Attribution to UNC4736 remains at medium-to-high confidence pending completion of Mandiant’s forensic investigation.
