Incident Report: Kelp DAO rsETH Bridge Exploit
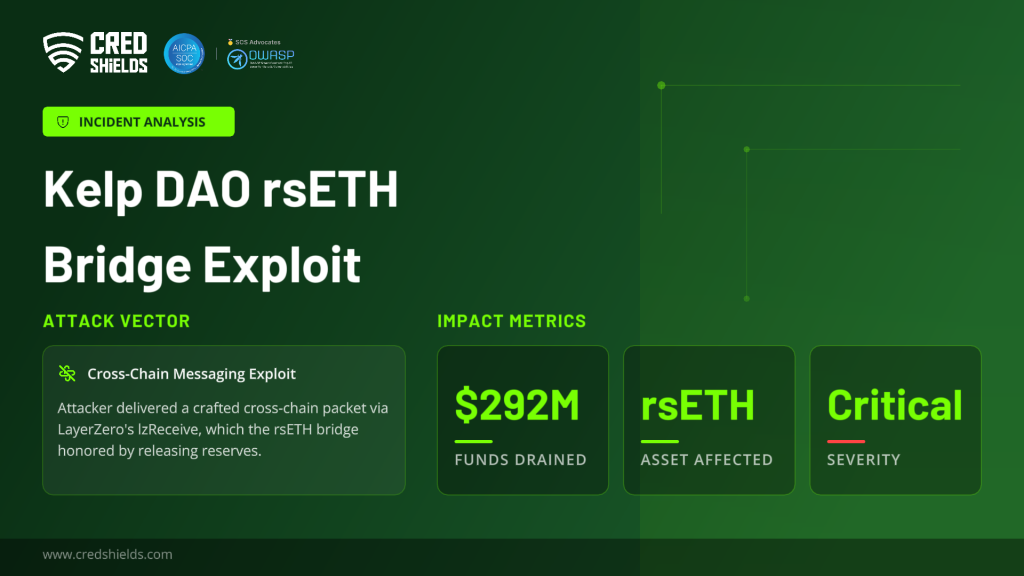
Incident: Kelp DAO rsETH bridge, April 18 2026, 17:35 UTC
An attacker pulled 116,500 rsETH roughly $292M, about 18% of the ~630,000-token supply out of Kelp DAO’s LayerZero-backed rsETH bridge. As far as we can tell that makes it the largest DeFi loss of 2026 to date.
From the trace so far, the failure sits at the cross-chain messaging boundary: a forged inbound instruction was accepted as valid and Kelp’s bridge honored it by releasing reserves. Whether the break is in the messaging layer, the verifier config, or Kelp’s own acceptance logic is still open.
The saving grace is response time. Kelp hit pauseAll 46 minutes after the first drain, which caught
two follow-ups queued behind the main one another ~$200M that never left.
Incident Timeline
| Time | Event |
|---|---|
| Pre-incident | Attacker funded operational wallets via Tornado Cash to obscure gas origin |
| 17:35 | Attacker calls lzReceive on LayerZero’s EndpointV2 contract with a crafted packet. 116,500 rsETH (~$292M) is released from Kelp’s bridge to an attacker-controlled address |
| ~17:52 | Suspicious outflows flagged publicly by on-chain investigator ZachXBT |
| 18:21 | Kelp DAO emergency multisig executes pauseAll across core contracts |
| 18:26 | Attacker attempts second drain (~40,000 rsETH / ~$100M), reverted |
| 18:28 | Attacker attempts third drain (~40,000 rsETH / ~$100M), reverted |
| 18:30–20:00 | Partner protocols (Aave, SparkLend, Fluid, Lido, Ethena) initiate precautionary freezes |
| 20:10 | Kelp DAO publicly acknowledges “suspicious cross-chain activity” |
Technical Analysis
Attack surface
Kelp runs a liquid restaking protocol: ETH in, routed through EigenLayer for restaking yield, rsETH out as the liquid receipt. To get rsETH onto chains beyond mainnet, they stood up a LayerZero bridge reserves on Ethereum, wrapped rsETH on 20-plus other chains.
Exploit mechanics
The attacker called lzReceive on LayerZero’s EndpointV2. That’s the hook the executor uses to deliver a message into the destination contract once the configured DVNs have signed off.
In this case the bridge accepted the packet as a valid cross-chain instruction, and 116,500 rsETH went out. Where the break actually sits verifier config, a DVN, Kelp’s own input validation, or something in the seams between them is what Kelp, LayerZero, Unichain, and the auditors they’ve pulled in are still pulling apart.
Follow-ups that didn’t land
At 18:26 and 18:28 UTC the attacker fired the same shape of transaction again, twice, each aiming for roughly 40,000 rsETH (~$100M a pop). Both reverted. Kelp’s emergency multisig had hit pauseAll at 18:21 LRT Deposit Pool, withdrawal module, oracle, the rsETH contract itself, all frozen.
So: 46 minutes from first drain to pause, and ~$200M that didn’t leave. The full pitch for investing in a pause stack you never actually want to have to use.
Laundering tradecraft
The operational wallets were pre-funded out of Tornado Cash. That tells you this was prepared, not opportunistic someone was sitting on cold wallets waiting for go-time. Per Cyvers, the loot was swapped back to ETH and split between Ethereum and Arbitrum. Two liquid chains, picked on purpose: harder to freeze, messier to trace.
Systemic Impact
Direct impact
The real worry right now is rsETH’s peg and what’s actually underneath it. The drained reserves were the collateral for wrapped rsETH on 20-plus chains, so if you’re holding rsETH on an L2, you genuinely don’t know whether your token still has backing. The ugly scenario is the feedback loop: people panic-redeem on L2s, that squeezes the mainnet supply that wasn’t touched, Kelp gets forced to start unwinding restaking positions to cover withdrawals, and the unwinds themselves make the hole bigger.
Contagion across DeFi
The downstream response was the one thing that actually went right in the first 24 hours. Aave froze rsETH markets on v3 and v4 almost immediately; Stani confirmed Aave’s own contracts were fine and noted rsETH had no borrowing power on the platform to begin with. SparkLend and Fluid froze theirs too. Lido paused new deposits into earnETH their rsETH-exposed product and went out of their way to say stETH, wstETH, and core Lido were not touched. Ethena paused its LayerZero OFT bridges out of Ethereum as a precaution, with no direct rsETH exposure and still over 101% collateralization.
Market reaction
AAVE took about a 10% hit as markets priced in bad-debt risk. stETH and wstETH dropped ~4% on general LRT/LST jitters. rsETH itself traded with a wobbly peg; liquidity got thin fast.
Root Cause (Preliminary)
No full RCA has been published yet. From what’s visible on-chain, the break lives somewhere in the trust boundary between LayerZero’s message verification and Kelp’s bridge acceptance logic which half of that boundary actually failed is the whole question.
A few things to pin down before drawing conclusions: whether a DVN or verifier configuration was compromised or just misconfigured, whether Kelp’s own packet validation has a flaw sitting downstream of LayerZero’s checks, and whether some cryptographic or replay-protection assumption everyone was quietly trusting didn’t actually hold. Those aren’t the same bug, and they imply very different fixes.
Kelp says the RCA is being run jointly with LayerZero, Unichain, their auditors, and outside security help.
Lessons and Recommendations
For LRT and bridge operators
The structural problem is concentration. A single reserve pool sitting underneath wrapped rsETH on 20-plus chains looks like capital efficiency and behaves like one-click systemic risk. Splitting reserves per chain, or at least per cluster, costs some efficiency but keeps a breach local instead of ecosystem-wide. That trade is worth making.
Kelp’s 46-minute pause saved roughly $200M. Few security investments come with that kind of expected return. The work itself is unglamorous a multisig that can actually be assembled at 2am on a Sunday, pause procedures that have been rehearsed, a real on-call rotation but it’s what decided whether this was a $292M incident or closer to $500M. That said, 46 minutes is a long time at this TVL. Automated outflow circuit breakers would cut response from minutes to seconds and are worth the engineering cost.
On the bridge itself: the underlying messaging protocol shouldn’t be the only layer standing between an attacker and the reserves. Input validation at the bridge, outflow caps, rate limits any one of them feels redundant, all of them together would have meaningfully bounded this loss even with the LayerZero-side failure.
For downstream integrators
Aave, Spark, Fluid, and Lido could move that fast because they’d already built freeze paths for third-party assets in peacetime. That readiness can’t be improvised once a drain is underway by then the posture is reactive, not containing.
Ethena’s “we have no exposure” post did real work too. In the middle of an incident, silence reads as something to hide. Fast, specific statements including “we’re fine, here’s why” noticeably reduce how much contagion gets priced into adjacent assets. Put plainly: they stop people dumping tokens that had nothing to do with what happened.
For the broader ecosystem
Cross-chain messaging has quietly become one of the most consequential surfaces in DeFi, and it’s not close anymore. As more LRTs and wrapped assets spread across L2s and alt-L1s, one bad bridge day eats a proportionally larger share of the ecosystem. Whether the next one sits on LayerZero, Wormhole, CCIP, or a new stack almost doesn’t matter the pattern does.
A nine-figure incident of this shape in 2026 is unlikely to be the last.
This analysis is based on public on-chain data, official statements from Kelp DAO, LayerZero, Aave, Lido, Ethena, SparkLend, and Fluid as of April 19, 2026.

