During TOKEN2049 week, one of the biggest global events in Web3, we ran a series of Twitter polls, to understand how the community thinks about audits, accountability, trust, and security practices.
And the results? They speak volumes. Across 7 polls, we gathered over 4,000+ cumulative views and 300+ participant votes, representing founders, auditors, developers, and investors. These micro-surveys offered a real pulse check on how the Web3 community perceives security standards, and we found one recurring theme:
Security is seen as critical, but often sidelined, misunderstood, or oversimplified.
Let’s unpack what the blockchain community really thinks.
How Long Does an Audit Remain “Reliable”?
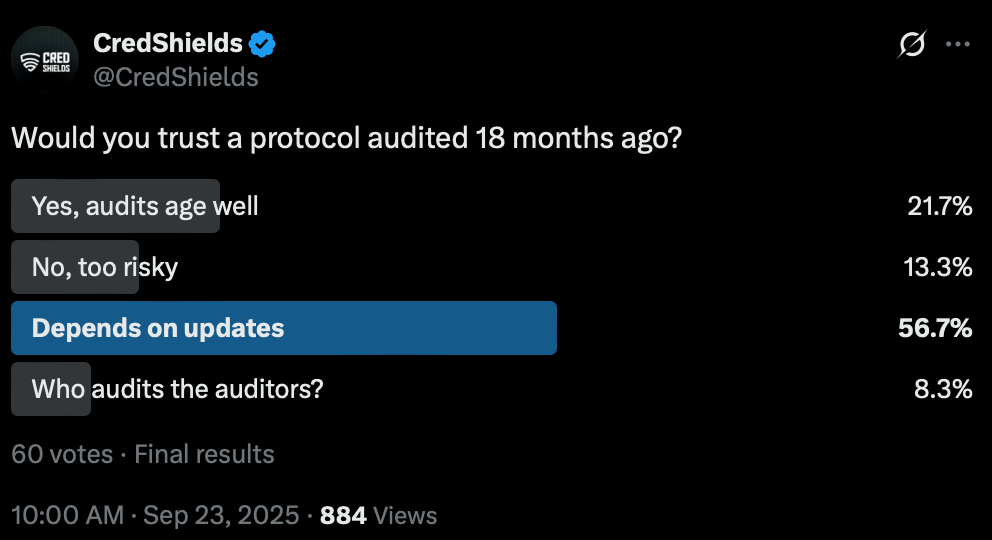
- 56.7% said it depends on code updates, but only 21.7% said “Yes”
- 13.3% also considered it “Too risky”
In a separate poll:
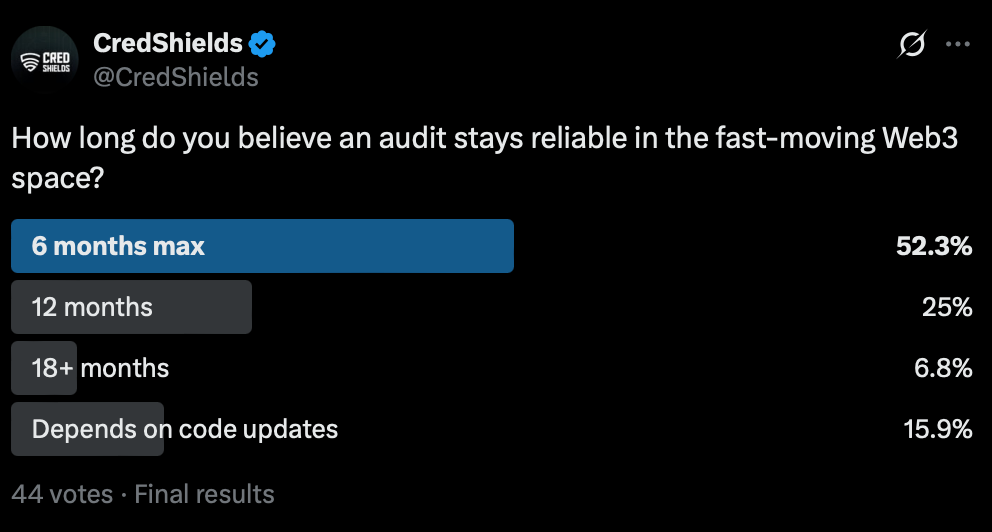
- 52.3% said 6 months max and 25% had faith on 12 months timeline
- 15.9% believed that it depends on code updates
Takeaway: Audits aren’t forever. The community overwhelmingly believes that security reviews must evolve with the code. One static report won’t cut it in a dynamic ecosystem.
When an Exploit Happens!! Who Pays? Who’s Responsible?
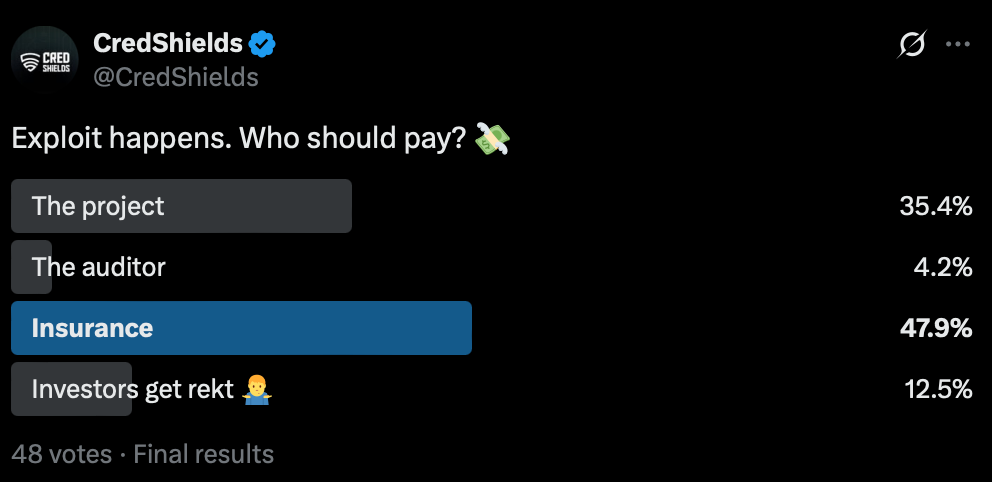
- 47.9% voted Insurance given there is one which is very unlikely in Web3 space
- 35.4% simply blamed The Project and 12.5% agreed that Investors are on their own
- Only 4.2% pointed to The Auditor
However when it comes to being responsible, and held accountable
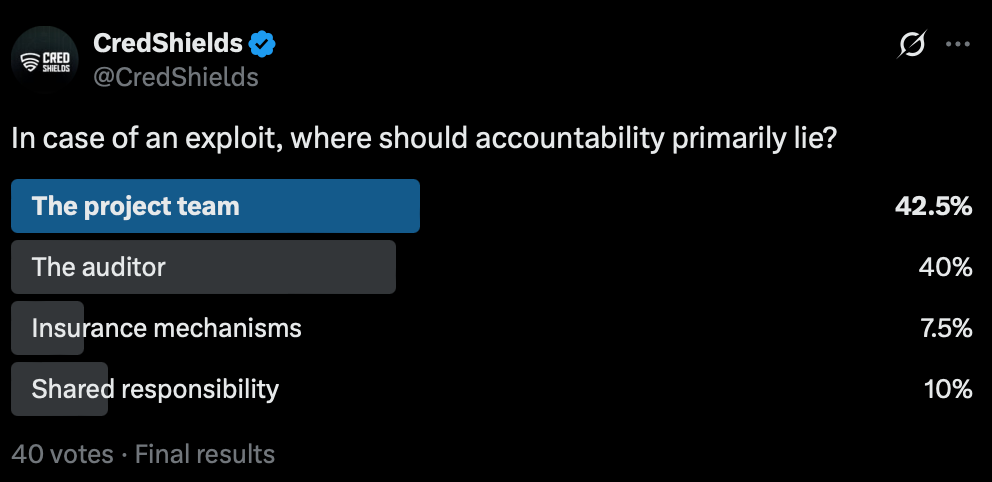
- 42.5% said Project team which highlights development phase
- 40% blamed the Auditors and held them accountable
- However, 10% believe it should be shared responsibility
Takeaway: Most participants still expect project teams to shoulder the lion’s share of responsibility in the event of an exploit, followed closely by auditors. However, nearly half the respondents demand external financial safeguards like insurance. This signals a growing appetite for post-audit protection, not just pre-deployment prevention.
Security can’t be a one-time checkbox, it must be a continuous, evaluative process from development to deployment and beyond.
Audit Badges: Trust Signal or Marketing Gimmick?

- 46.9% said that it depends on the auditor
- 40.8% believe it is Real protection
- 6.1% consider it just as a Marketing flex
Another poll mirrored this:
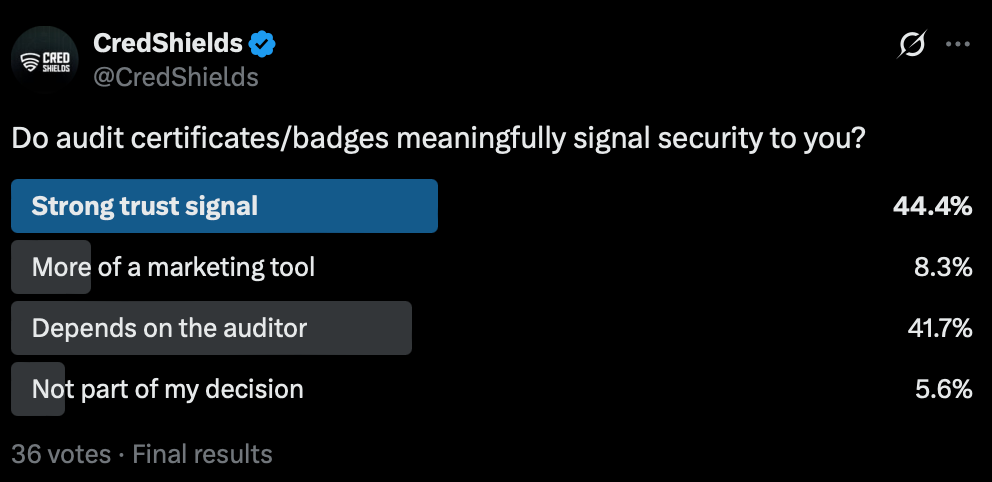
- 44.4% saw audit certificates as a strong trust signal
- 41.7% said it depends on who audited, but only 8.3% saw them as purely marketing
Takeaway: In an industry flooded with “audit badges,” credibility is king. It’s not about having a badge, it’s about who issued it, how thorough it was, and what followed after.
Are Projects Actually Implementing Audit Recommendations?
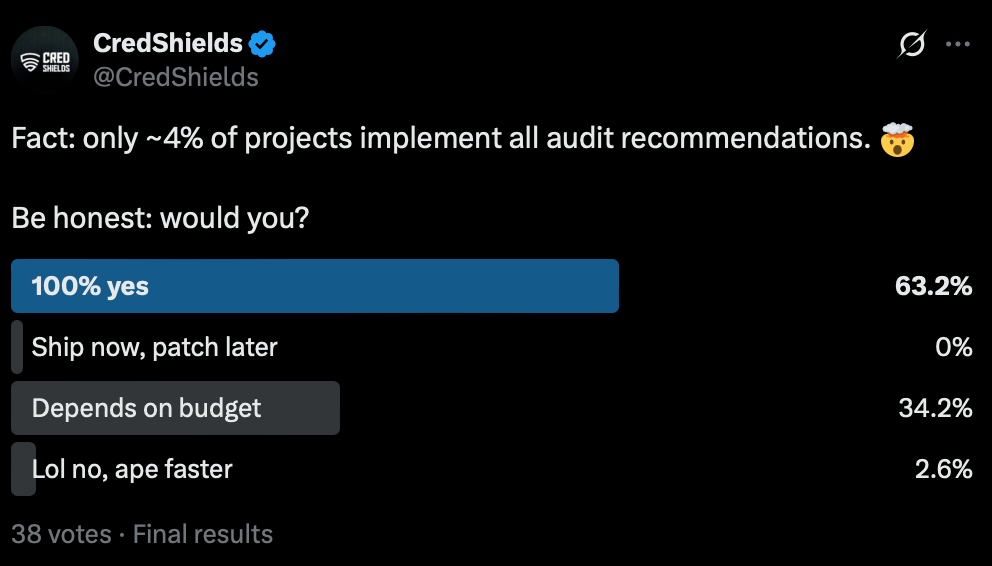
- 63.2% said that they would implement all audit recommendations
- However 34.2% admitted it depends on budget too
- 0% chose “ship now, patch later”
Takeaway: The intent to secure the project is there, but budget and time pressure still derail full remediation. There’s a gap between intent and execution, and it needs to be bridged by better security tools, education, and automation.
The Bigger Picture: Security is Evolving
From our week-long campaign, here’s what we’ve learned:
- Security is not a one-time checkbox, it’s a lifecycle.
- The community wants transparency from both projects and auditors.
- There’s growing interest in insurance, continuous audits, and auditor credibility.
- Audit reports without implementation are half-baked security.
Where CredShields Stands
We believe securing Web3 isn’t just about completing just another checklist, it’s about:
- Providing AI-powered continuous scanning via SolidityScan
- Offering manual audits with deep context and 3-month free retesting
- Ensuring our audit badge actually means something
- Partnering with development tools to close the intent vs. implementation gap
Thanks to everyone who voted, commented, and reshared our polls. Let’s keep asking tough questions and pushing for higher standards.Want to secure your smart contract? Try a free scan on SolidityScan or get in touch.
