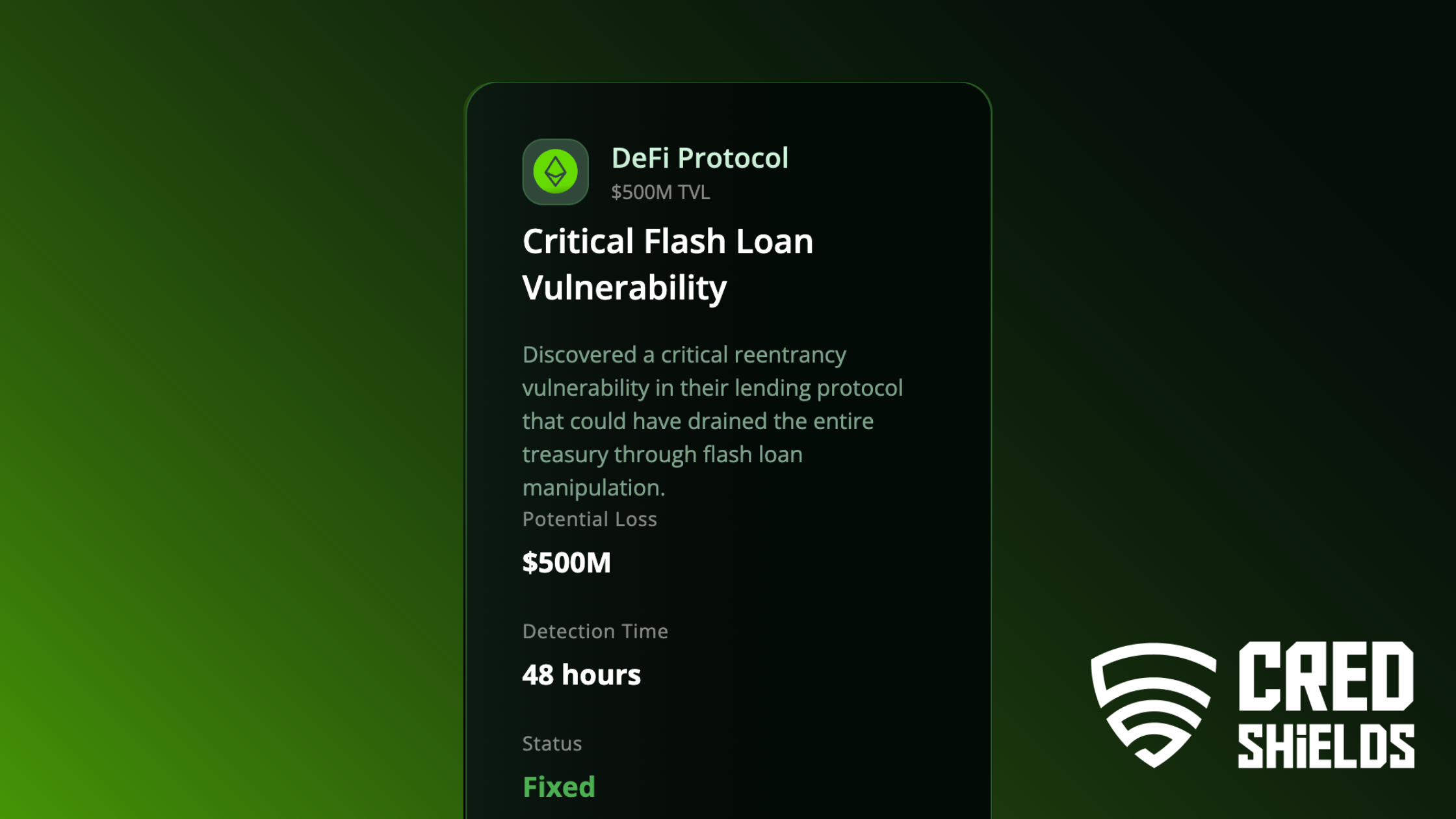
Executive Summary
A DeFi lending protocol with over $500M TVL faced an undetected reentrancy + flash-loan attack vector capable of draining the entire treasury in a single transaction. CredShields discovered the vulnerability within 48 hours, helped the protocol implement a fix, and validated the resolution through a full post-patch audit.
Background
As lending protocols scale, integrations, new assets, liquid pools, collateral types often introduce hidden trust boundaries. In this case, multiple pooled assets were recently added, but the original contract architecture had not undergone a full security review after these expansions.
This created an opportunity for attackers to chain flash-loan calls with state inconsistencies across the borrowing lifecycle.
The Problem
During scheduled monitoring, the protocol noticed anomalies in balance updates. While the anomalies did not trigger a live exploit, they indicated the possibility of:
Potential Attack Impact
- Full treasury drainage
- Insolvency of the lending pool
- Complete loss of user collateral
- Liquidity collapse across all asset pairs
- Cross-protocol contagion (due to multi-DEX dependencies)
Root Cause
A reentrancy gap in the lending logic allowed state-dependent checks to be bypassed during multi-leg flash-loan operations.
CredShields’ Approach
CredShields executed an accelerated AI-assisted + manual audit cycle, focusing on:
Flash-loan lifecycle analysis
- Borrow → manipulate → repay loops
- Cross-contract call ordering
State-consistency validation
- Balance updates
- Mapping integrity
- Event sequencing
Threat simulations
Reproducing real attack patterns used in:
- Euler Finance exploit
- bZx flash-loan exploit
- Mango Markets manipulation
Fallback and reentrancy review
- On-chain multi-call contexts
- Missing mutex/locking patterns
Technical Breakdown: What We Found
CredShields uncovered:
1. A multi-call reentrancy vector
Attackers could invoke a deposit-borrow-repay sequence while balances were mid-update.
2. Incorrect ordering of internal accounting steps
The protocol updated balances after external calls, enabling manipulation windows.
3. Flash-loan price manipulation surface
Due to asynchronous price feed updates during high-frequency loops.
Potential Loss: $500M+
This was a full protocol-kill vulnerability.
Outcome
- Vulnerability patched within 24 hours of disclosure
- Full architecture rewrite of the relevant module
- New invariant tests embedded into CI/CD
- On-chain monitoring rules updated
- Post-fix audit validated no bypass paths remained
Final Status: Fixed
The protocol avoided what could have been one of the largest DeFi losses recorded.
Industry Lessons Learned
1. Flash-loan functionality must be treated as adversarial by default.
Even minor logic gaps can cascade into treasury-level threats.
2. Reentrancy risks reappear when new assets or integrations are added.
Architecture must be re-evaluated after major feature expansions.
3. Automated scanners alone cannot catch multi-call vulnerabilities.
Hybrid manual + AI threat modeling is essential.
Additional Read: