Executive Summary
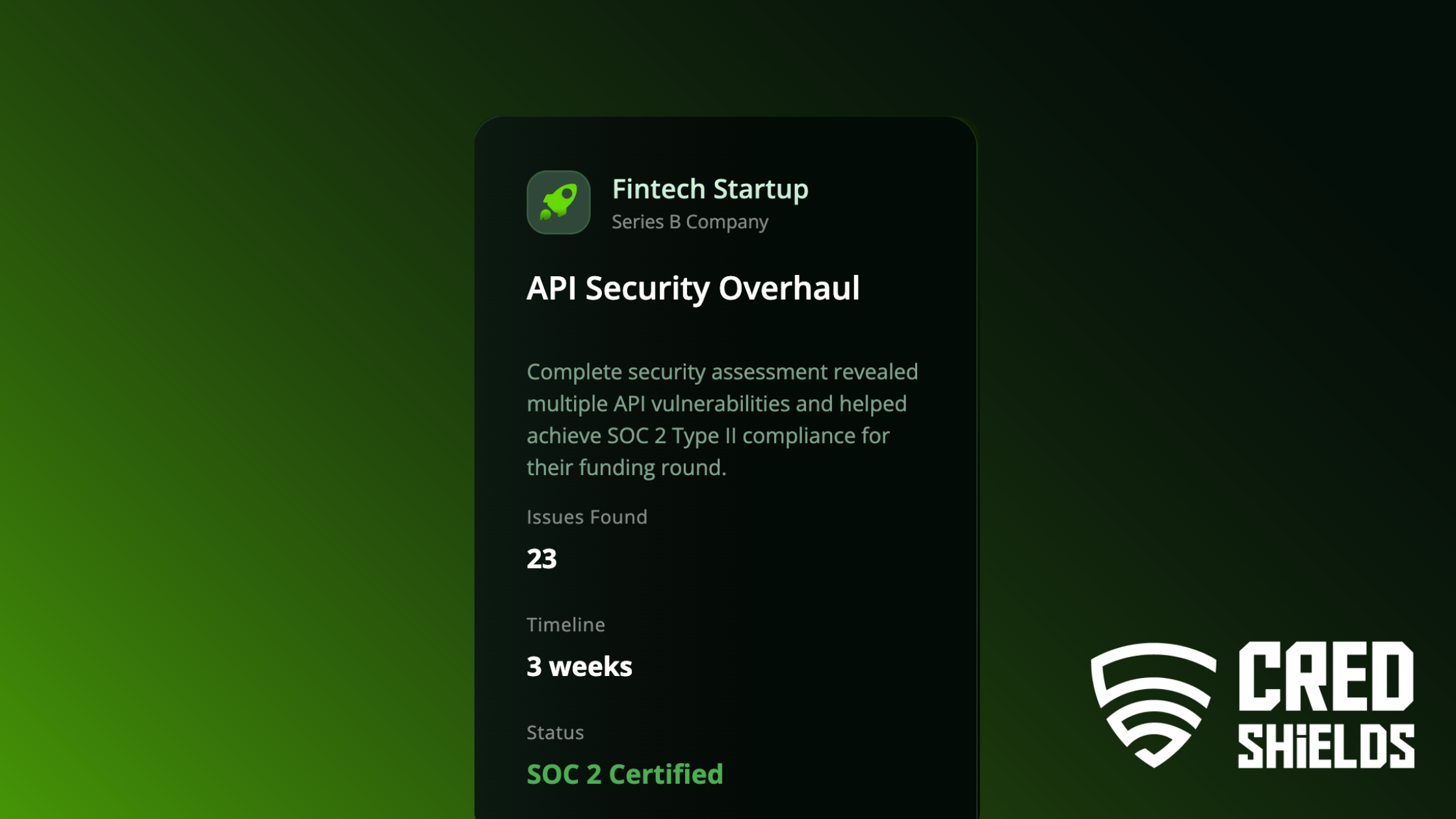
A Series B fintech startup preparing for its next funding round needed to demonstrate enterprise-grade API security and compliance. CredShields uncovered 23 critical vulnerabilities, implemented an end-to-end remediation program, and guided the client to successful SOC 2 Type II certification all within 3 weeks.
Background
As the startup scaled rapidly, its API ecosystem grew to include:
- Customer apps
- Partner integrations
- Internal microservices
- Operational dashboards
However, the growth outpaced the team’s ability to standardize security controls, leaving gaps in authorization logic, token handling, and abuse prevention.
The Problem
Key Risks Identified
- Broken access control across multiple endpoints
- IDOR (Insecure Direct Object Reference) vulnerabilities exposing sensitive user data
- Weak token management allowing session persistence
- Exposed debug endpoints leaking metadata
- Absence of rate limiting, enabling brute-force and enumeration attacks
- Insufficient logging and auditability, a direct blocker for SOC 2
Why This Was Critical
The company was entering investor due-diligence, where API security posture is one of the largest deal-breakers in fintech.
CredShields’ Approach
1. Full API Surface Discovery
Mapped every endpoint across staging and production.
2. Manual logic testing
Uncovered business-logic exploits that automated scanners cannot detect.
3. SOC 2 alignment gap analysis
Evaluated system design, monitoring, and access control frameworks.
4. Secure SDLC integration
Implemented new workflows for:
- Threat modeling
- Code review standards
- Access control schemas
- API governance policies
5. Engineering enablement
Conducted workshops and training for the internal team to ensure long-term compliance.
Technical Breakdown
We identified:
- 6 IDOR vulnerabilities
- 5 Broken Authorization cases
- 3 token lifecycle flaws
- 2 unsecured admin endpoints
- Multiple missing validation and sanitization layers
Total Issues Found: 23
Timeline: 3 weeks
Outcome
- All issues remediated within the engagement period
- SOC 2 Type II audit passed successfully
- The company secured its funding round
- Engineering teams adopted a stable, compliant API architecture framework
Final Status: SOC 2 Certified
Industry Lessons Learned
Scaling APIs without governance leads directly to compliance debt.
Security must be standardized across teams, not implemented piecemeal.
SOC 2 is not just documentation, it requires technical hardening.
Business logic vulnerabilities are the most damaging yet least detectable.
Additional Read